gentoo系统中安装配置sendmail邮件服务器和dovecot收件器
先说需要安装哪些软件,因为使用的平台是Gentoo 操作系统,所以就用gentoo 的安装方式
1 :安装dns 域名服务器,如果你在公网,并且有自已的域名,那么不用自已安装域名服务器,( 因为邮件服务器要用到域名的解析,反向解析,所以要安装,我尝试用ip 地址代替邮箱域名,失败,所以必须装)
emerge bind bind-tools 版本没要求,默认就行
2安装sendmail
USE='' mbox ssl" emerge sendmail
要加上mbox ssl 两个标记,以便让sendmail 支持mbox的邮件存储方式(就是在/var/mail 目录上存不同用户的邮件,而不是在各个用户的~目录下,) 另外还有一个sasl 的标记,不加也可以,好像sendmail 从某个版本对于ssl 的支持不需要sasl 了, 当前的sendmail 是mail-mta/sendmail-8.14.4
3 要用到openssl 库,在进行安全的ssl 连接时,需要用它生成几个文件,好像是证书之类,不太懂,但得装上
emerge -av openssl
4 安装dovecot
USE="ssl maildir mbox" emerge dovecot
确保ssl maildir mbox 这几个标记的存在,
sendmail 只负责发邮件,要想收邮件,要用到dovecot
下面是具体的安装过程
一安装并配置bind
sendmail 要用到域名解析,反向域名解析,所以要选安装dns 服务器bind,安装方法及配置见
http://blog.csdn.net/jixiuffff/archive/2009/11/07/4782285.aspx
简要摘写如下
/etc/bind/named.conf
[c-sharp] view plain copy
options {
directory "/var/bind";
// uncomment the following lines to turn on DNS forwarding,
// and change the forwarding ip address(es) :
//forward first;
//forwarders {
// 123.123.123.123;
// 123.123.123.123;
//};
listen-on-v6 { none; };
// 注释掉这行
// listen-on { 127.0.0.1; };
// listen-on { 127.0.0.1;192.168.1.2; };
// to allow only specific hosts to use the DNS server:
//allow-query {
// 127.0.0.1;
//};
// if you have problems and are behind a firewall:
//query-source address * port 53;
pid-file "/var/run/named/named.pid";
};
// Briefly, a zone which has been declared delegation-only will be effectively
// limited to containing NS RRs for subdomains, but no actual data beyond its
// own apex (for example, its SOA RR and apex NS RRset). This can be used to
// filter out "wildcard" or "synthesized" data from NAT boxes or from
// authoritative name servers whose undelegated (in-zone) data is of no
// interest.
// See http://www.isc.org/products/BIND/delegation-only.html for more info
//zone "COM" { type delegation-only; };
//zone "NET" { type delegation-only; };
zone "." IN {
type hint;
file "named.cache";
};
zone "localhost" IN {
type master;
file "pri/localhost.zone";
allow-update { none; };
notify no;
};
zone "127.in-addr.arpa" IN {
type master;
file "pri/127.zone";
allow-update { none; };
notify no;
};
//vi /etc/conf.d/hostname
//hostname="jixiuf.org"
//主机名为jixiuf.org
//我的ip是192.168.1.2 ,
//pri/jixiuf.org.zone 是/etc/bin/pri/jixiuf.org.zone
//实际是/var/bind/pri/目录的一个软链接
//此文件进行正向域名解析 ,由域名得ip
zone "jixiuf.org" IN {
type master;
file "pri/jixiuf.org.zone";
allow-update { none; };
notify no;
};
//此文件进行反向域名解析,由ip 得域名
zone "192.in-addr.arpa" IN {
type master;
file "pri/jixiuf_r.zone";
allow-update { none; };
notify no;
};
# Use with the following in named.conf, adjusting the allow list as neede
# key "rndc-key" {
# algorithm hmac-md5;
# secret "kGKuKdPDjzvUPgJPncVZxw==";
# };
#
# controls {
# inet 127.0.0.1 port 953
# allow { 127.0.0.1; } keys { "rndc-key"; };
# };
# End of named.conf
jf pri # cat /var/bind/pri/jixiuf.org.zone
jixiuf.org 的正向解析文件
[c-sharp] view plain copy
$TTL 1W
@ IN SOA jixiuf.org. root.jixiuf.org. (
2010092203 ; Serial
28800 ; Refresh
14400 ; Retry
604800 ; Expire - 1 week
86400 ) ; Minimum
@ IN NS jixiuf.org.
@ IN A 192.168.1.2
;三个别名mail.jixiuf.org. smtp.jixiuf.org. pop3.jixiuf.org. 实际上都是jixiuf.org.的别名,它们具有相同的ip 192.168.1.2
mail IN CNAME jixiuf.org.
smtp IN CNAME jixiuf.org.
pop3 IN CNAME jixiuf.org.
@ IN MX 5 mail.jixiuf.org.
/var/bind/pri/localhost.zone ,默认即可
反向解析文件
jf pri # cat /var/bind/pri/jixiuf_r.zone
[c-sharp] view plain copy
$ORIGIN 192.in-addr.arpa.
$TTL 1W
@ 1D IN SOA jixiuf.org. root.jixiuf.org. (
2010092204 ; serial
3H ; refresh
15M ; retry
1W ; expiry
1D ) ; minimum
; @ 在这里相当于 jixiuf
@ 1D IN NS jixiuf.org.
;192.168.1.2 解析为jixiuf.org. 及mail.jixiuf.org. ....
2.1.168 1D IN PTR jixiuf.org.
2.1.168 1D IN PTR mail.jixiuf.org.
2.1.168 1D IN PTR smtp.jixiuf.org.
2.1.168 1D IN PTR pop3.jixiuf.org.
测试一下是否成功
正向解析
jixiuf pri # host smtp.jixiuf.org
smtp.jixiuf.org is an alias for jixiuf.org.
jixiuf.org has address 192.168.1.2
jixiuf.org mail is handled by 5 mail.jixiuf.org.
jixiuf pri # host pop3.jixiuf.org
pop3.jixiuf.org is an alias for jixiuf.org.
jixiuf.org has address 192.168.1.2
jixiuf.org mail is handled by 5 mail.jixiuf.org.
jixiuf pri # host mail.jixiuf.org
mail.jixiuf.org is an alias for jixiuf.org.
jixiuf.org has address 192.168.1.2
jixiuf.org mail is handled by 5 mail.jixiuf.org.
jixiuf pri # host jixiuf.org
jixiuf.org has address 192.168.1.2
jixiuf.org mail is handled by 5 mail.jixiuf.org.
反向解析
jixiuf pri # nslookup 192.168.1.2
Server: 127.0.0.1
Address: 127.0.0.1#53
2.1.168.192.in-addr.arpa name = pop3.jixiuf.org.
2.1.168.192.in-addr.arpa name = jixiuf.org.
2.1.168.192.in-addr.arpa name = mail.jixiuf.org.
2.1.168.192.in-addr.arpa name = smtp.jixiuf.org.
jixiuf pri #
==========================================================================================================
下面是关于sendmail 的了
1 添加两个测试用户
useradd -m -g mail -s /bin/false mail1
useradd -g mail -s /bin/false mail2
passwd mail1
passwd mail2
mail1 有/home/mail1 目录,而mail2 没有
为mail1 mail2 起个别名, 不起也可以
/etc/mail/aliases
[c-sharp] view plain copy
zhang3: mail1
li4: mail2
manager: mail1, mail2
# zhang3@jixiuf.org means mail1@jixiuf.org
#and mail send to manager@jixiuf.org will be send to mail1@jixiuf.org and mail@jixiuf.org
然后运行命令newaliases
编辑 /etc/mail/access
[c-sharp] view plain copy
127.0.0.1 RELAY
#192.168.1.2 RELAY
mail.jixiuf.org RELAY
jixiuf.org RELAY
然后运行 makemap hash <access access.db
表示发送到jixiuf.org mail.jixiuf.org 地址的信才给传送,其他地址的不送
/etc/init.d/sendmail start
此时sendmail 已经可以发信了,但是不能向外网关邮件,因为外网的邮箱服务器无法以我们的ip进行域名反解析(好像是,不太清楚)
在同一网段找另外一台机器,当然用虚拟机也可以(网络桥接)用Outlook Express 发mail1@jixiuf.org manager@jixiuf.org 发送邮件 ,
smtp pop3 服务器都填写成mail.jixiuf.org 或者jixiuf.org 也可以
但是此时sendmail 发信不支持ssl 连接,所以用户名密码很容易被人监听到
下面进行sendmail 发件通过ssl
在/etc/mail/sendmail.mc 中添加
[c-sharp] view plain copy
TRUST_AUTH_MECH("EXTERNAL DIGEST-MD5 CRAM-MD5 LOGIN PLAIN")dnl
define(`confAUTH_MECHANISMS', `EXTERNAL DIGEST-MD5 CRAM-MD5 LOGIN PLAIN GSSAPI KERBEROS_V4')dnl
dnl define(`CERT_DIR', `MAIL_SETTINGS_DIR`'certs')dnl
define(`CERT_DIR', `/etc/mail/certs')dnl
define(`confCACERT_PATH', `CERT_DIR')dnl
define(`confCACERT', `CERT_DIR/cacert.pem')dnl 1
define(`confSERVER_CERT', `CERT_DIR/cert.pem')dnl 2
define(`confSERVER_KEY', `CERT_DIR/key.pem')dnl 3
define(`confCLIENT_CERT', `CERT_DIR/cert.pem')dnl
define(`confCLIENT_KEY', `CERT_DIR/key.pem')dnl
然后运行
m4 sendmail.mc >sendmail.cf
接下来需要生成证书 这个过程不必理解,
生成的过程
http://www.worldhello.net/doc/email_howto/ar01s01s09.html
从这篇文章的 1.9.7. 配置 sendmail — 证书管理 做就可以
摘录如下:
$ mkdir /tmp/CA
$ cd /tmp/CA
$ mkdir certs crl newcerts private
$ echo "01" > serial
$ cp /dev/null index.txt
$ cp /usr/local/openssl/openssl.cnf.sample openssl.cnf
改成cp /etc/ssl/openssl.cnf openssl.cnf
$ vi openssl.cnf (set values) 这一步主要修改openssl.cnf 文件中
dir = ./demoCA # Where everything is kept
改成
dir = /tmp/CA #修改成我们实际的目录
$ openssl req -new -x509 -keyout private/cakey.pem -out cacert.pem -days 365 -config openssl.cnf
$ openssl req -nodes -new -x509 -keyout newreq.pem -out newreq.pem -days 365 -config openssl.cnf
$ openssl x509 -x509toreq -in newreq.pem -signkey newreq.pem -out tmp.pem
$ openssl ca -config openssl.cnf -policy policy_anything -out newcert.pem -infiles tmp.pem
$ rm -f tmp.pem
手动修改生成的 newreq.pem文件
Remove the unsigned certificate (leaving the private key 删除证书部分,只保留私钥部分
mkdir /etc/mail/certs
cp cacert.pem /etc/mail/certs/cacert.pem
cp newreq.pem /etc/mail/certs/key.pem
cp newcert.pem /etc/mail/certs/cert.pem
cd /etc/mail/certs/
chmod 400 key.pem
Check key properties
$ openssl x509 -noout -in cacert.pem -text
Make sure that the CN of the CA certificate and CN of the server
certificate are different, because newer versions of Mozilla and
Netscape won't accept the server certificate if it is self-signed
这句不理解,
/etc/init.d/sendmail restart
1 :安装dns 域名服务器,如果你在公网,并且有自已的域名,那么不用自已安装域名服务器,( 因为邮件服务器要用到域名的解析,反向解析,所以要安装,我尝试用ip 地址代替邮箱域名,失败,所以必须装)
emerge bind bind-tools 版本没要求,默认就行
2安装sendmail
USE='' mbox ssl" emerge sendmail
要加上mbox ssl 两个标记,以便让sendmail 支持mbox的邮件存储方式(就是在/var/mail 目录上存不同用户的邮件,而不是在各个用户的~目录下,) 另外还有一个sasl 的标记,不加也可以,好像sendmail 从某个版本对于ssl 的支持不需要sasl 了, 当前的sendmail 是mail-mta/sendmail-8.14.4
3 要用到openssl 库,在进行安全的ssl 连接时,需要用它生成几个文件,好像是证书之类,不太懂,但得装上
emerge -av openssl
4 安装dovecot
USE="ssl maildir mbox" emerge dovecot
确保ssl maildir mbox 这几个标记的存在,
sendmail 只负责发邮件,要想收邮件,要用到dovecot
下面是具体的安装过程
一安装并配置bind
sendmail 要用到域名解析,反向域名解析,所以要选安装dns 服务器bind,安装方法及配置见
http://blog.csdn.net/jixiuffff/archive/2009/11/07/4782285.aspx
简要摘写如下
/etc/bind/named.conf
[c-sharp] view plain copy
options {
directory "/var/bind";
// uncomment the following lines to turn on DNS forwarding,
// and change the forwarding ip address(es) :
//forward first;
//forwarders {
// 123.123.123.123;
// 123.123.123.123;
//};
listen-on-v6 { none; };
// 注释掉这行
// listen-on { 127.0.0.1; };
// listen-on { 127.0.0.1;192.168.1.2; };
// to allow only specific hosts to use the DNS server:
//allow-query {
// 127.0.0.1;
//};
// if you have problems and are behind a firewall:
//query-source address * port 53;
pid-file "/var/run/named/named.pid";
};
// Briefly, a zone which has been declared delegation-only will be effectively
// limited to containing NS RRs for subdomains, but no actual data beyond its
// own apex (for example, its SOA RR and apex NS RRset). This can be used to
// filter out "wildcard" or "synthesized" data from NAT boxes or from
// authoritative name servers whose undelegated (in-zone) data is of no
// interest.
// See http://www.isc.org/products/BIND/delegation-only.html for more info
//zone "COM" { type delegation-only; };
//zone "NET" { type delegation-only; };
zone "." IN {
type hint;
file "named.cache";
};
zone "localhost" IN {
type master;
file "pri/localhost.zone";
allow-update { none; };
notify no;
};
zone "127.in-addr.arpa" IN {
type master;
file "pri/127.zone";
allow-update { none; };
notify no;
};
//vi /etc/conf.d/hostname
//hostname="jixiuf.org"
//主机名为jixiuf.org
//我的ip是192.168.1.2 ,
//pri/jixiuf.org.zone 是/etc/bin/pri/jixiuf.org.zone
//实际是/var/bind/pri/目录的一个软链接
//此文件进行正向域名解析 ,由域名得ip
zone "jixiuf.org" IN {
type master;
file "pri/jixiuf.org.zone";
allow-update { none; };
notify no;
};
//此文件进行反向域名解析,由ip 得域名
zone "192.in-addr.arpa" IN {
type master;
file "pri/jixiuf_r.zone";
allow-update { none; };
notify no;
};
# Use with the following in named.conf, adjusting the allow list as neede
# key "rndc-key" {
# algorithm hmac-md5;
# secret "kGKuKdPDjzvUPgJPncVZxw==";
# };
#
# controls {
# inet 127.0.0.1 port 953
# allow { 127.0.0.1; } keys { "rndc-key"; };
# };
# End of named.conf
jf pri # cat /var/bind/pri/jixiuf.org.zone
jixiuf.org 的正向解析文件
[c-sharp] view plain copy
$TTL 1W
@ IN SOA jixiuf.org. root.jixiuf.org. (
2010092203 ; Serial
28800 ; Refresh
14400 ; Retry
604800 ; Expire - 1 week
86400 ) ; Minimum
@ IN NS jixiuf.org.
@ IN A 192.168.1.2
;三个别名mail.jixiuf.org. smtp.jixiuf.org. pop3.jixiuf.org. 实际上都是jixiuf.org.的别名,它们具有相同的ip 192.168.1.2
mail IN CNAME jixiuf.org.
smtp IN CNAME jixiuf.org.
pop3 IN CNAME jixiuf.org.
@ IN MX 5 mail.jixiuf.org.
/var/bind/pri/localhost.zone ,默认即可
反向解析文件
jf pri # cat /var/bind/pri/jixiuf_r.zone
[c-sharp] view plain copy
$ORIGIN 192.in-addr.arpa.
$TTL 1W
@ 1D IN SOA jixiuf.org. root.jixiuf.org. (
2010092204 ; serial
3H ; refresh
15M ; retry
1W ; expiry
1D ) ; minimum
; @ 在这里相当于 jixiuf
@ 1D IN NS jixiuf.org.
;192.168.1.2 解析为jixiuf.org. 及mail.jixiuf.org. ....
2.1.168 1D IN PTR jixiuf.org.
2.1.168 1D IN PTR mail.jixiuf.org.
2.1.168 1D IN PTR smtp.jixiuf.org.
2.1.168 1D IN PTR pop3.jixiuf.org.
测试一下是否成功
正向解析
jixiuf pri # host smtp.jixiuf.org
smtp.jixiuf.org is an alias for jixiuf.org.
jixiuf.org has address 192.168.1.2
jixiuf.org mail is handled by 5 mail.jixiuf.org.
jixiuf pri # host pop3.jixiuf.org
pop3.jixiuf.org is an alias for jixiuf.org.
jixiuf.org has address 192.168.1.2
jixiuf.org mail is handled by 5 mail.jixiuf.org.
jixiuf pri # host mail.jixiuf.org
mail.jixiuf.org is an alias for jixiuf.org.
jixiuf.org has address 192.168.1.2
jixiuf.org mail is handled by 5 mail.jixiuf.org.
jixiuf pri # host jixiuf.org
jixiuf.org has address 192.168.1.2
jixiuf.org mail is handled by 5 mail.jixiuf.org.
反向解析
jixiuf pri # nslookup 192.168.1.2
Server: 127.0.0.1
Address: 127.0.0.1#53
2.1.168.192.in-addr.arpa name = pop3.jixiuf.org.
2.1.168.192.in-addr.arpa name = jixiuf.org.
2.1.168.192.in-addr.arpa name = mail.jixiuf.org.
2.1.168.192.in-addr.arpa name = smtp.jixiuf.org.
jixiuf pri #
==========================================================================================================
下面是关于sendmail 的了
1 添加两个测试用户
useradd -m -g mail -s /bin/false mail1
useradd -g mail -s /bin/false mail2
passwd mail1
passwd mail2
mail1 有/home/mail1 目录,而mail2 没有
为mail1 mail2 起个别名, 不起也可以
/etc/mail/aliases
[c-sharp] view plain copy
zhang3: mail1
li4: mail2
manager: mail1, mail2
# zhang3@jixiuf.org means mail1@jixiuf.org
#and mail send to manager@jixiuf.org will be send to mail1@jixiuf.org and mail@jixiuf.org
然后运行命令newaliases
编辑 /etc/mail/access
[c-sharp] view plain copy
127.0.0.1 RELAY
#192.168.1.2 RELAY
mail.jixiuf.org RELAY
jixiuf.org RELAY
然后运行 makemap hash <access access.db
表示发送到jixiuf.org mail.jixiuf.org 地址的信才给传送,其他地址的不送
/etc/init.d/sendmail start
此时sendmail 已经可以发信了,但是不能向外网关邮件,因为外网的邮箱服务器无法以我们的ip进行域名反解析(好像是,不太清楚)
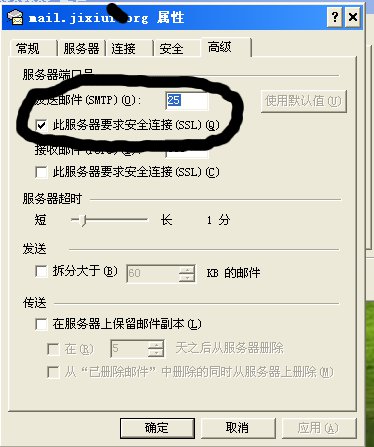
在同一网段找另外一台机器,当然用虚拟机也可以(网络桥接)用Outlook Express 发mail1@jixiuf.org manager@jixiuf.org 发送邮件 ,
smtp pop3 服务器都填写成mail.jixiuf.org 或者jixiuf.org 也可以
但是此时sendmail 发信不支持ssl 连接,所以用户名密码很容易被人监听到
下面进行sendmail 发件通过ssl
在/etc/mail/sendmail.mc 中添加
[c-sharp] view plain copy
TRUST_AUTH_MECH("EXTERNAL DIGEST-MD5 CRAM-MD5 LOGIN PLAIN")dnl
define(`confAUTH_MECHANISMS', `EXTERNAL DIGEST-MD5 CRAM-MD5 LOGIN PLAIN GSSAPI KERBEROS_V4')dnl
dnl define(`CERT_DIR', `MAIL_SETTINGS_DIR`'certs')dnl
define(`CERT_DIR', `/etc/mail/certs')dnl
define(`confCACERT_PATH', `CERT_DIR')dnl
define(`confCACERT', `CERT_DIR/cacert.pem')dnl 1
define(`confSERVER_CERT', `CERT_DIR/cert.pem')dnl 2
define(`confSERVER_KEY', `CERT_DIR/key.pem')dnl 3
define(`confCLIENT_CERT', `CERT_DIR/cert.pem')dnl
define(`confCLIENT_KEY', `CERT_DIR/key.pem')dnl
然后运行
m4 sendmail.mc >sendmail.cf
接下来需要生成证书 这个过程不必理解,
生成的过程
http://www.worldhello.net/doc/email_howto/ar01s01s09.html
从这篇文章的 1.9.7. 配置 sendmail — 证书管理 做就可以
摘录如下:
$ mkdir /tmp/CA
$ cd /tmp/CA
$ mkdir certs crl newcerts private
$ echo "01" > serial
$ cp /dev/null index.txt
$ cp /usr/local/openssl/openssl.cnf.sample openssl.cnf
改成cp /etc/ssl/openssl.cnf openssl.cnf
$ vi openssl.cnf (set values) 这一步主要修改openssl.cnf 文件中
dir = ./demoCA # Where everything is kept
改成
dir = /tmp/CA #修改成我们实际的目录
$ openssl req -new -x509 -keyout private/cakey.pem -out cacert.pem -days 365 -config openssl.cnf
$ openssl req -nodes -new -x509 -keyout newreq.pem -out newreq.pem -days 365 -config openssl.cnf
$ openssl x509 -x509toreq -in newreq.pem -signkey newreq.pem -out tmp.pem
$ openssl ca -config openssl.cnf -policy policy_anything -out newcert.pem -infiles tmp.pem
$ rm -f tmp.pem
手动修改生成的 newreq.pem文件
Remove the unsigned certificate (leaving the private key 删除证书部分,只保留私钥部分
mkdir /etc/mail/certs
cp cacert.pem /etc/mail/certs/cacert.pem
cp newreq.pem /etc/mail/certs/key.pem
cp newcert.pem /etc/mail/certs/cert.pem
cd /etc/mail/certs/
chmod 400 key.pem
Check key properties
$ openssl x509 -noout -in cacert.pem -text
Make sure that the CN of the CA certificate and CN of the server
certificate are different, because newer versions of Mozilla and
Netscape won't accept the server certificate if it is self-signed
这句不理解,
/etc/init.d/sendmail restart
现在可以通过安全的ssl 进行认证了.